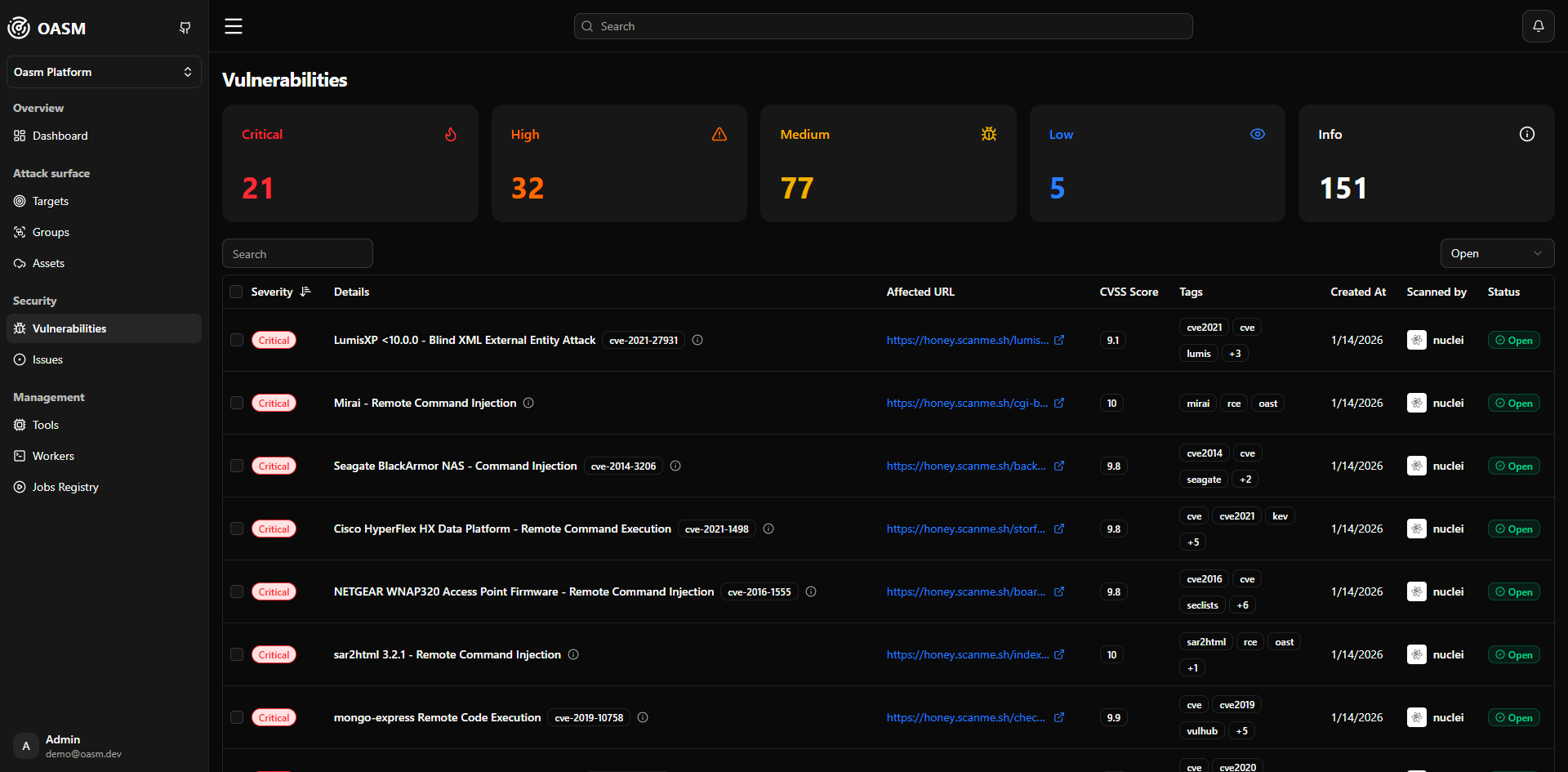
The Vulnerability module provides a centralized interface to monitor, analyze, and manage all detected security findings across your assets. It aggregates results from scanning tools and presents them in a structured way, allowing you to quickly identify risks, investigate details, and take action.Documentation Index
Fetch the complete documentation index at: https://docs.oasm.dev/llms.txt
Use this file to discover all available pages before exploring further.
Overview
At the top of the page, vulnerabilities are summarized by severity:- Critical
- High
- Medium
- Low
- Info
- Severity — Risk level of the finding
- Details — Name of the vulnerability or detection
- Affected URL — The endpoint where the issue was found
- CVSS Score — Standardized risk score (if available)
- Tags — Categories such as
ssl,dns,discovery, etc. - Created At — Timestamp when the issue was detected
- Scanned by — Tool used for detection (e.g., nuclei)
- Status — Current state (e.g., Open)
Search and filtering
You can refine the vulnerability list using:- Search bar — Find by domain, vulnerability name, or keyword
- Severity filter — Focus on specific risk levels
- Status filter — Track open or resolved issues
- Date filter — Narrow down results by time
View vulnerability details
To inspect a vulnerability in depth:- Locate a vulnerability in the table
- Click on the Details column (vulnerability name)
Vulnerability detail panel
The detail view provides comprehensive information for investigation.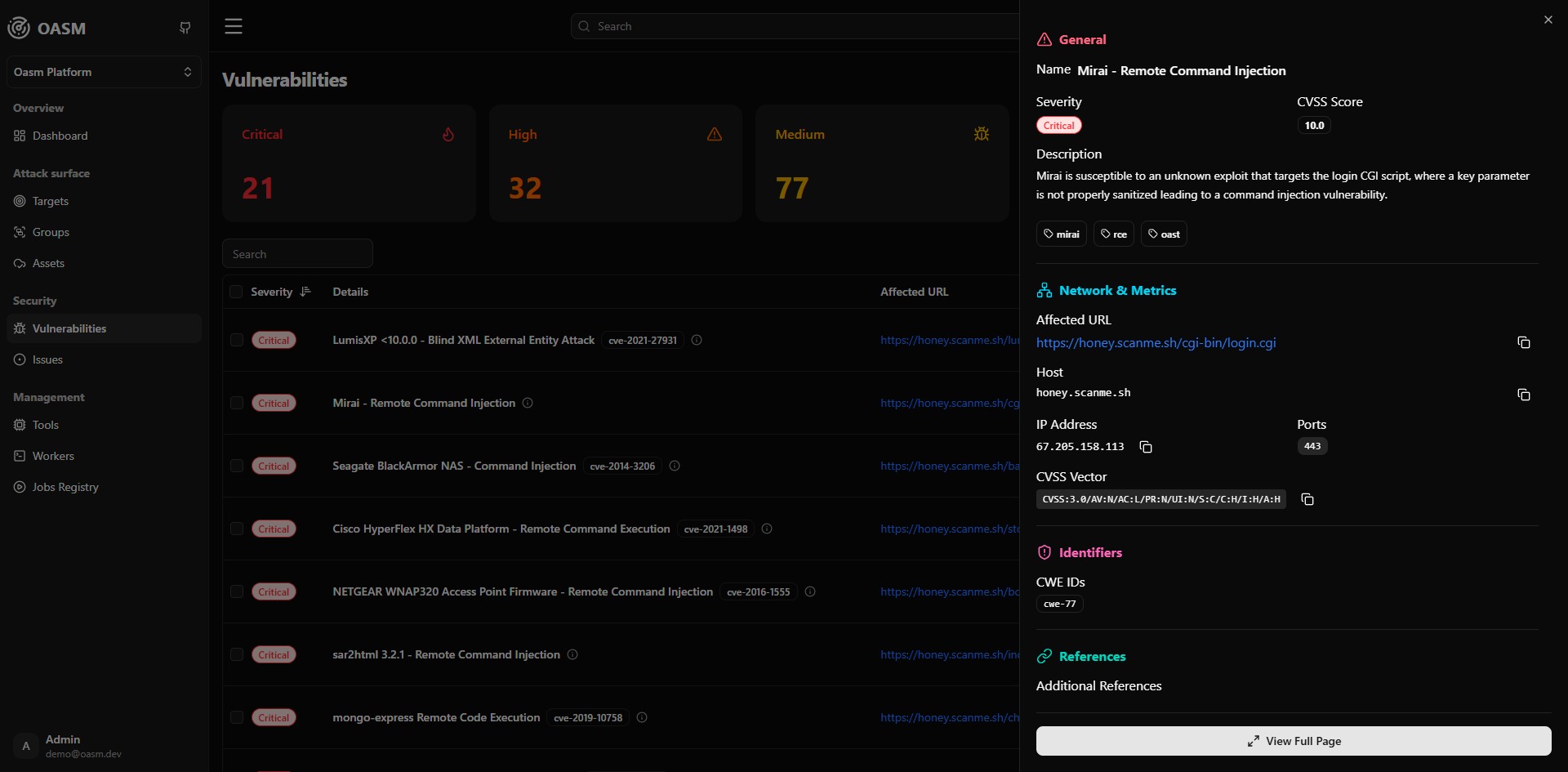
General
- Name — Detection name (e.g., TLS Version - Detect)
- Severity — Risk classification
- Description — Explanation of the issue and its security implications
- Tags — Technical categories
Network & Metrics
- Affected URL — Full endpoint (including port if applicable)
- Host — domain or asset
- IP Address — Resolved IP address
- Ports — Open or scanned ports related to the finding
Vulnerabilities are automatically generated from scans executed via configured tools and schedules in targets or groups.